Key Personal & Research (Non-Work) Projects
Workshops Instructed
An introductory workshop covering the fundamental concepts of cybersecurity, including threat actors, attack vectors, and defensive strategies. Participants learned to identify common risks and apply basic security measures.
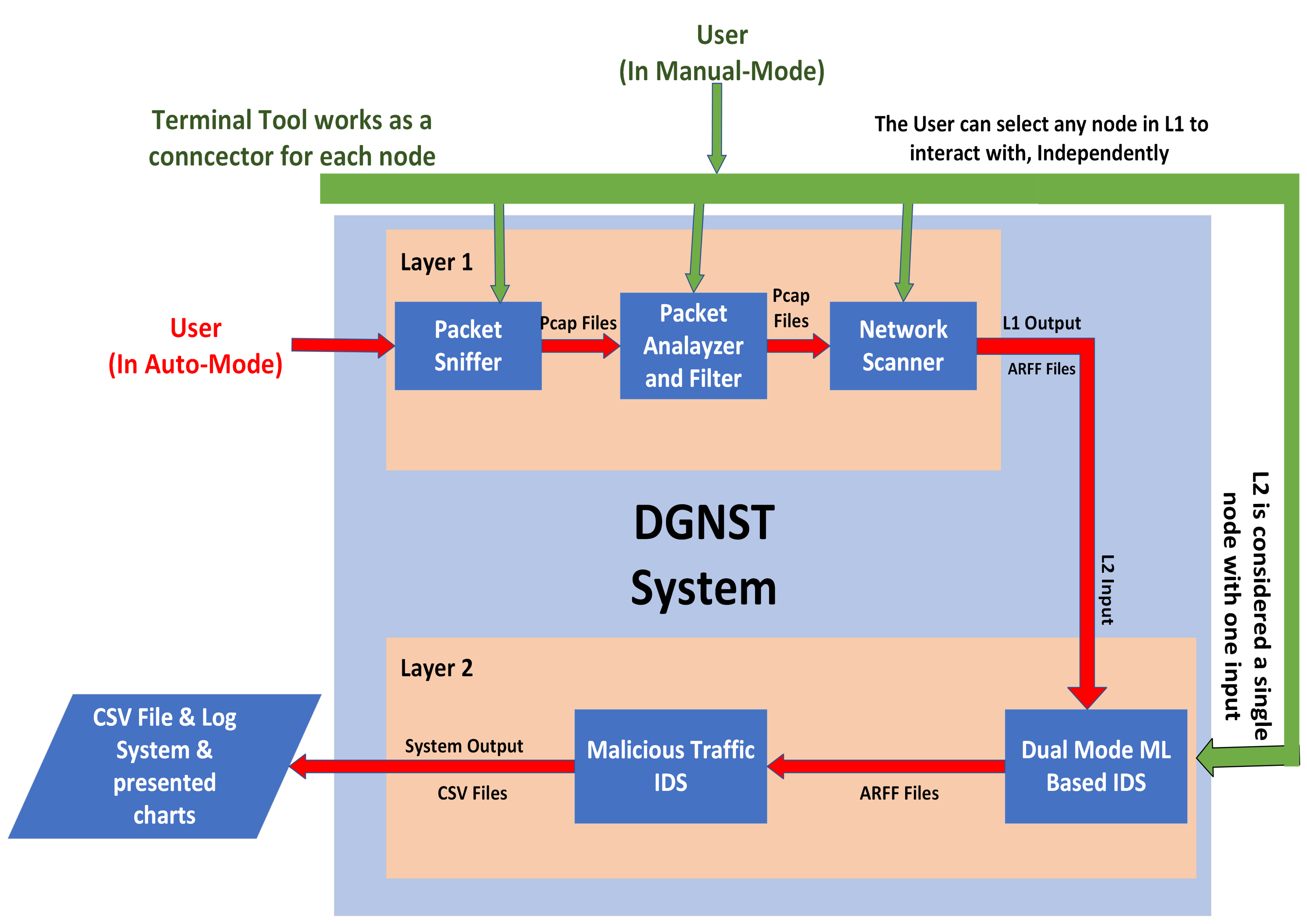
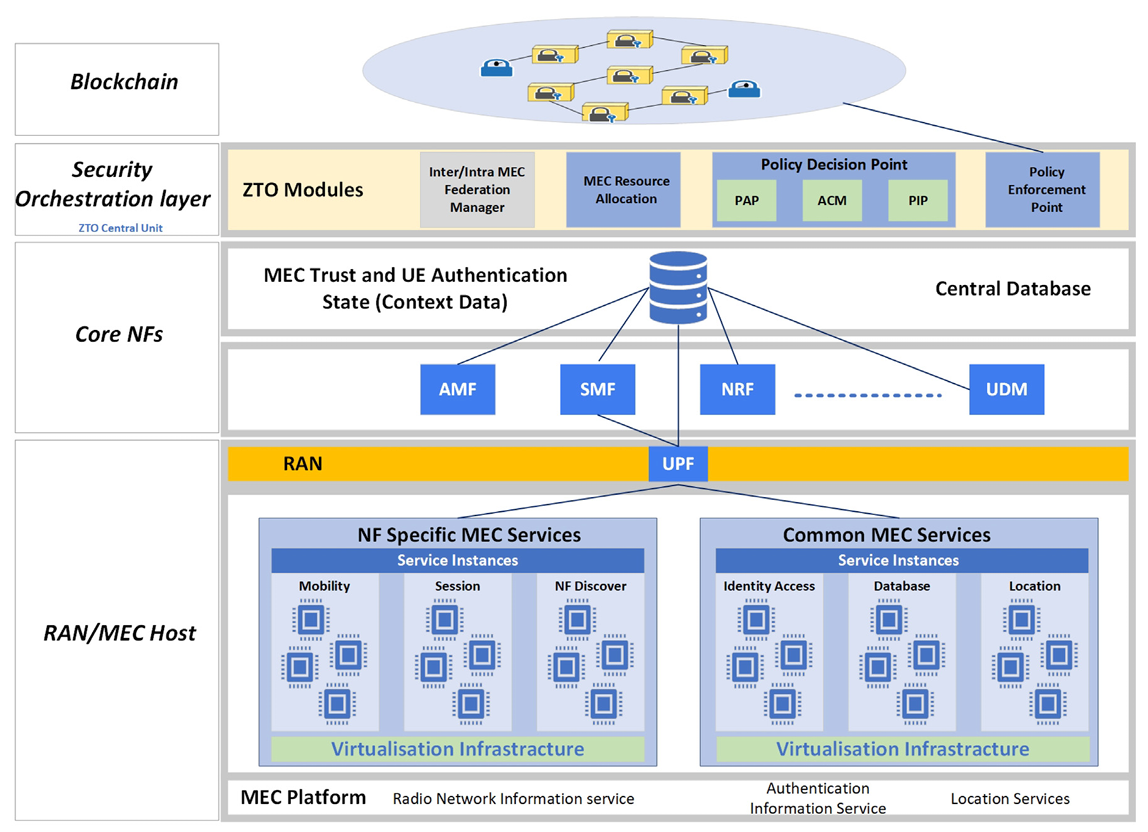
A deep dive into network security protocols, firewall configuration, and intrusion detection systems. This hands-on workshop provided practical experience in securing enterprise-level networks against sophisticated attacks.
Participants explored the methodologies and tools used by ethical hackers to identify and exploit vulnerabilities in systems. The workshop emphasized responsible disclosure and defensive countermeasures.
Explore the building blocks of the internet. This course covers the OSI and TCP/IP models, network protocols, and how data travels across the globe, providing a crucial foundation for any tech field.
Learn to defend the digital highways. This workshop introduces key concepts like firewalls, VPNs, and intrusion detection systems, teaching you how to protect networks from common cyber threats.
A tour of the ethical hacker's essential toolkit. This session provides a hands-on introduction to the Kali Linux environment and its powerful suite of tools for security assessments and penetration testing.
Delve into how programs use memory. This course explains concepts like the stack, heap, and pointers in an engaging way, revealing how understanding memory is key to both software development and security.
Unlock the power of supercomputing. This workshop introduces the world of High Performance Computing, parallel processing, and how to manage complex jobs using the SLURM workload manager.
An ethical exploration of game security and reverse engineering. This course teaches how to analyze game code to find bugs and vulnerabilities, contributing to game security and bug bounty programs.
Become a digital detective. This fast-paced course covers the fundamentals of digital forensics, including evidence acquisition, data recovery, and analysis of digital artifacts to uncover what happened on a device.
An academic look into the mechanics of aiming assists in games. This session explores the computer vision and mathematical principles involved, providing insight into how anti-cheat systems detect such tools.
Discover the surprising role of statistics in security. Learn how probabilistic models are used in everything from spam filtering and anomaly detection to cryptographic analysis and risk assessment.
Learn the fundamental principles of computer hardware through interactive challenges. This course gamifies the concepts of logic gates, circuits, and Boolean algebra to make learning fun and intuitive.
Volunteering Experience

IEEE
CPES
Programming Club

Kuwait Cybersecurity Centre

Sustainability Club